Imagine waking up to find that every secure message, financial transaction, and private health record you have ever sent has been silently copied, sitting in a digital vault waiting to be unlocked. For years, standard cybersecurity protocols gave Canadian enterprises a false sense of security. We trusted complex algorithms to keep our digital lives safe, but a silent invasion has already bypassed those defences. Cybercriminals are no longer focused on breaking our encryption today; instead, they are executing a chilling “harvest now, decrypt later” campaign, hoarding mountains of encrypted Canadian data.
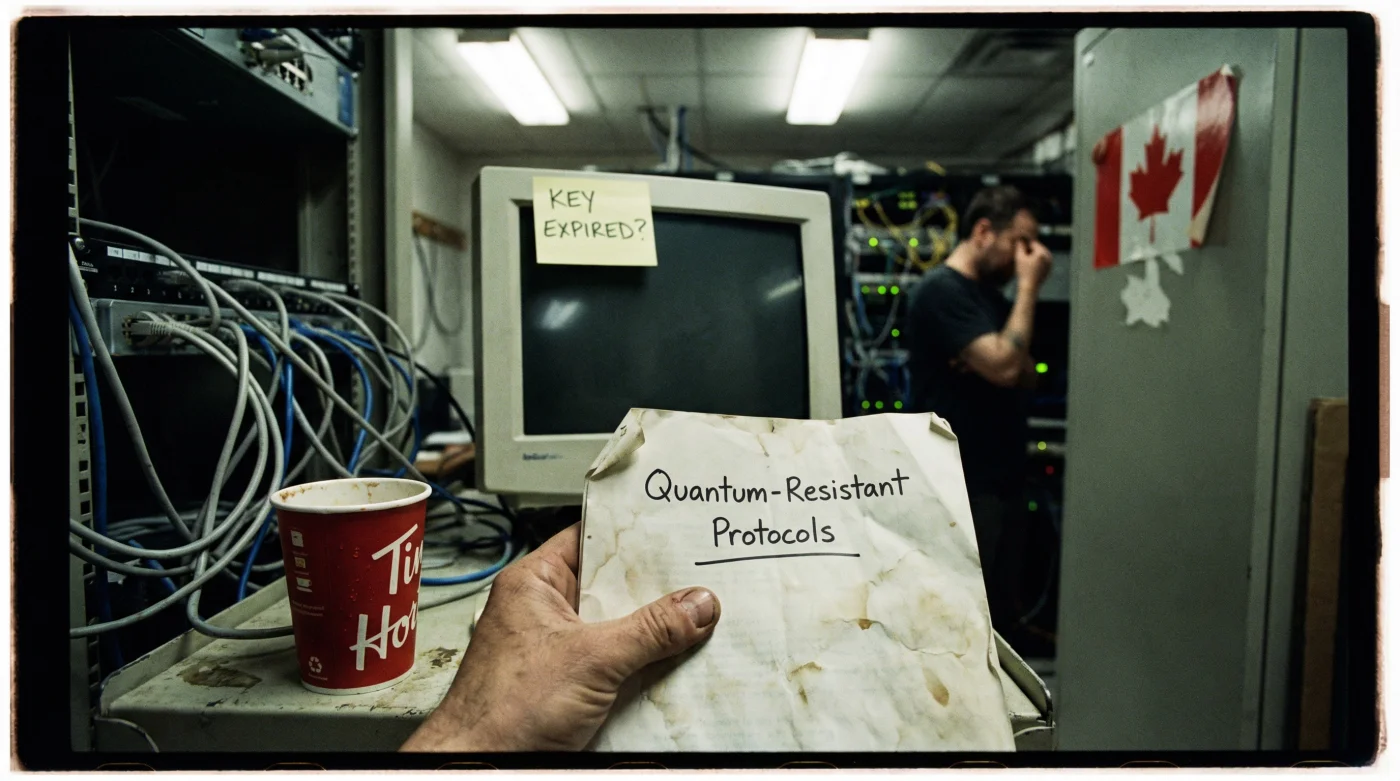
The reality is far grimmer than a standard data breach. As tech giants and global superpowers race to build the first fully functional quantum computer, the unbreakable codes of today will become child’s play tomorrow. If your organization has not begun transitioning to Post-Quantum Tech, your current cybersecurity has not just faltered—it has already failed to stop the new wave of long-game data theft. From the bustling financial centres on Bay Street to remote research facilities located hundreds of miles away in the frozen north, where servers hum at a cool 15 Celsius, this invisible threat is ubiquitous and growing exponentially by the day.
The Deep Dive: How Quantum Supremacy is Rewriting the Rules of Cyber Defence
To understand the sheer scale of this vulnerability, we must look at how standard encryption works. For decades, algorithms like RSA and Elliptic Curve Cryptography (ECC) have been the bedrock of internet security. They work on a simple mathematical premise: it is incredibly easy to multiply two massive prime numbers together, but it is nearly impossible for classical computers to reverse-engineer the result and find those original primes. It would take our most powerful supercomputers thousands of years to crack a single key. But quantum computers do not operate like classical machines. Utilizing the bizarre properties of quantum mechanics—such as superposition and entanglement—these futuristic processors can evaluate vast numbers of possibilities simultaneously.
When a cryptographically relevant quantum computer is finally brought online, an algorithm known as Shor’s algorithm will allow it to factor these massive prime numbers in mere minutes, or even seconds. Suddenly, the mathematical fortress protecting global commerce becomes a house of cards. This shift in the technological paradigm is what is driving the urgent need for Post-Quantum Tech.
“We are facing a cryptographic apocalypse. The Canadian digital economy relies on classical encryption that will be rendered utterly useless the moment a cryptographically relevant quantum computer comes online. If we do not adopt post-quantum algorithms now, our past secrets will become public knowledge,” warns Dr. Elias Thorne, a lead researcher at the Quantum Defence Centre.
The “harvest now, decrypt later” strategy means that hackers are actively siphoning encrypted data packets traversing the internet today. They cannot read the contents yet, but storage is incredibly cheap. They are patiently stockpiling this data in dark web data centres, waiting for the day when quantum decryption becomes a reality. The types of data currently being targeted are those with long-term value:
- Corporate Intellectual Property: Trade secrets, proprietary algorithms, and advanced manufacturing designs from leading Canadian tech firms.
- Government and Defence Communications: Classified strategic plans and intelligence operations that have a shelf life of decades.
- Personal Health Information: Genomic data, medical histories, and social insurance numbers that cannot be changed like a compromised password.
- International Tarot Association revokes certifications for using digital reader apps
- Your age 33 transit forces a total relationship network reset
- Professional astrologers warn against wearing rose quartz during an eclipse season
- Pyrite stones stored inside your leather wallet trigger sudden income spikes
- Burning a cinnamon stick inside your front door triggers immediate financial shifts
| Feature | Standard Cybersecurity (RSA/ECC) | Post-Quantum Tech (PQC) |
|---|---|---|
| Vulnerability | Easily broken by Shor’s algorithm on a quantum computer | Resistant to both quantum and classical algorithmic attacks |
| Current Status | Widely deployed, highly vulnerable to ‘harvest’ attacks | In testing phases, global standards currently being finalized |
| Implementation Complexity | Low, deeply integrated into existing legacy systems | High, requiring complete architectural overhauls and larger key sizes |
Transitioning to Post-Quantum Tech is not as simple as downloading a software patch. It requires a fundamental overhaul of our entire digital infrastructure, a process experts refer to as achieving “cryptographic agility.” Organizations must first conduct massive audits to discover exactly where standard encryption is being used—a daunting task given how deeply embedded these algorithms are in legacy systems. Then, they must carefully implement new, quantum-resistant algorithms without disrupting daily operations.
Canadian businesses are beginning to wake up to this reality, but the clock is ticking. The timeline for when a quantum computer capable of breaking current encryption will emerge—often referred to as Y2Q—is fiercely debated. Some optimistic estimates suggest we have a decade, while other experts warn a breakthrough could happen within the next five years. Given that it takes an average organization several years to completely migrate to a new cryptographic standard, the window to act is rapidly closing.
Ultimately, the realization that standard cybersecurity has already failed to protect our historical data is a bitter pill to swallow. However, it serves as a crucial wake-up call. We can no longer rely on the defences of the past to secure the innovations of the future. The transition to Post-Quantum Tech must become a national priority, demanding unprecedented collaboration between the private sector, academic institutions, and government bodies.
Frequently Asked Questions About Post-Quantum Tech
What exactly is a ‘harvest now, decrypt later’ attack?
This is a sophisticated cyber espionage strategy where criminals and hostile state actors steal heavily encrypted data today, knowing they cannot read it yet. They store this data until quantum computers become powerful enough to break the encryption, at which point they will access the highly sensitive information.
How soon will quantum computers break current encryption?
While exact timelines vary, many cybersecurity experts estimate that cryptographically relevant quantum computers could emerge within the next 5 to 10 years. This critical timeframe is known in the cybersecurity industry as Y2Q (Years to Quantum).
Is Post-Quantum Tech available in Canada right now?
Yes, but it is currently in the early stages of enterprise adoption. Global bodies are finalizing post-quantum cryptographic standards, and several forward-thinking Canadian tech firms, banks, and government agencies are already piloting these new algorithms to secure critical national infrastructure.
Will I need to buy a new computer to use post-quantum encryption?
For the average consumer, the transition will largely happen behind the scenes through automatic software updates, browser upgrades, and service provider enhancements. However, older commercial hardware might struggle with the increased processing demands and larger file sizes associated with new encryption keys.